This lab will teach you how to model the CCNA lab topology in a WAN scale.
This lab assumes that you have already completed lab 1.
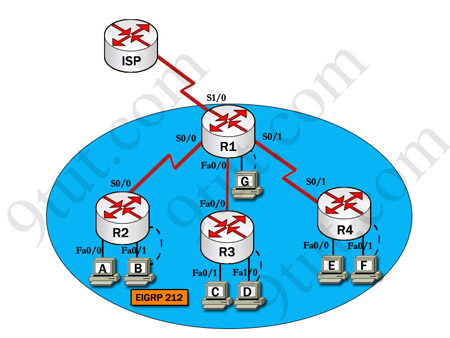
This is the topology used in the CCNA practical labs. Study the diagram to see the construct of this topology.
Creating the Project
Create a new project named ‘CCNA_Lab’ call the scenario ‘baseline’.
In the start-up wizard when choosing the network scale select the ‘choose from maps’ option and click ‘next’.
From the list of maps offered choose the ‘UK’ map and click ‘next’.
When selecting technologies for the project choose the Sm_Int_Model_List, ‘ethernet’ and ‘ethernet_advanced’ model groups and continue through the wizard until the project screen opens showing a map of the ‘UK’.
Placing Subnets on the Map
Select the ‘subnet’ object from the object palate and place four of them on the map as shown below.
Rename these subnets, Subnet_A, Subnet_B, Subnet_C and Subnet_DE. To do this ‘right-click’ over the Subnet and select the ‘Edit Attributes’ option then change the value in the name field and ‘click’ ‘Ok’.
It should now look like this.
The subnets are named after the routers they contain. Note how the subnet over London contains both routers D and E. On the lab topology these routers are connected together through a hub on a local network.
Subnet_A
To enter one of the subnets ‘double-click’ over it with the mouse. The project view will change to that of inside the subnet.
The first thing we need to do is place a router in the subnet. Change the object palate to the ‘Cisco’ Group.
Study the CCNA topology, the Lab_A router needs 2 Ethernet interfaces and one serial interface. We are going to use 1600 series Cisco routers in this topology, Find one with the appropriate interfaces, The CS_1605R_e2_s1 satisfies these demands, Place one inside the subnet then re name it Lab_A.
To rename the router ‘right-click’ and ‘Edit Attributes’ as with the subnet. Name the router Lab_A.
Now change the object palate back to the ‘CCNA-Lab-Baseline’ group and place 2 more subnets beside the router.
Rename the subnets ‘Switch_Subnet’ and ‘Hub_Subnet’ as shown below.
Now enter the Switch subnet by ‘double-clicking’ the icon.
Inside the switch subnet use the ‘configure rapid topology’ tool to create a star network topology the setting for which are shown below.
Rename the switch ‘Lab_A_Switch’.
Now go to the hub subnet and create another rapid configuration, this time using a 64-port Ethernet hub as the centre node and only 40 workstations. Don’t forget to rename the hub Lab_A_Hub.
Now return to subnet A. In the object palate select the 10BaseT link and connect the Router to each of the subnets. Before the link is created you will be prompted to select the node within each subnet to which it will connect. Connect through the nodes named Lab_A_Switch and Lab_A_Hub. See how that by naming the nodes we have made them easy to identify.
Subnet A should now like this:
Now go to Subnet B
This subnet requires a router with 2 serial interfaces and one Ethernet interface. Find the appropriate 1600 series router and place one in the subnet, re name it Lab_B. Now repeat the same rapid configuration as the in the lab B hub subnet. Name the hub Lab_B_Hub connect it to the router using a 10BaseT link. It should now look like this:
Now go to subnet B and repeat this topology remembering to name the Router Lab_B and the hub Lab_C_Hub.
To speed up this process you may wish to select all the nodes then use the ‘cut’ and ‘paste’ functions under the ‘Edit’ menu. The nodes can then be renamed.
Now go to subnet D.
This subnet will contain 2 routers, Lab D and lab E. Each requires 1 Ethernet interface and lab D requires 1 serial interface. Place the appropriate routers in the subnet then rename them Lab_D and Lab_E.
Now create another rapid configuration for a hub with 40 workstations as with the other subnets, rename the hub Lab_DE_Hub.
Now connect the lab D and E routers to the hub using 10BaseT links.
The finished subnet should look like this:
Now return to the map of the UK.
The next step is to connect the routers together. This will be done using 28K point-to-point protocol links.
Change the object panel to the links view. Now find the PPP 28K link and use it to connect each of the subnets. Each time a link is drawn you will be prompted to select the node to which the link attaches. Select the router for each subnet, the lab D router for subnet DE.
The completed network should look like this.
The Network we have Created
This network resembles that of a company with 4 offices operating in the UK. For this lab we will assume the company sells insurance over the phone. Subnet A is the head office. The head office is served by the 100 node switched network. This site also contains a sub office as subnets B,C and D. These are the call centres from where sales are made.
Our next step is to create some traffic for the network. In this scenario we will simulate the typical traffic used by a company. This is as follows:
Light e-mail – Used by staff to communicate with each other.
Light web browsing – An intranet is used to present staff with sales details.
Medium database access – An internal database will store the records used by staff to conduct day-to-day business operations.
A workgroup server will be attached to each hub to provide the local network with e-mail and intranet facilities.
A single server located at the head office in the Lab_A_switch subnet will provide database access to the entire company.
Adding Traffic to the Network
As you may remember from lab1 to add traffic to the network you need to define it through an application definition and a profile definition. From the CCNA_Lab-Baseline object palette find the two icons as pictured below and place them in the project workspace.
Not how this time we are not using pre-defined configs but we are going to define them ourselves.
Firstly we will define the application config telling Opnet which applications we are going to be using.
Right-click over the ‘Application Definition’ icon and choose to ‘Edit Attributes’ From the menu that appears.
Now click over the ‘value’ field next to the ‘Application Definitions’ attribute and select ‘edit’ from the popup menu.
The following window will appear:
In this table we will define our applications. As we want 3 types of application e-mail, web browsing and database we will need to enter 3 rows. Change the value in the rows box at the bottom left of the screen to 3. Three rows will now appear in the table.
We now have to enter our 3 applications.
For the first row ‘click’ the mouse over the description field and select ‘Edit’ from the drop down menu.
The first traffic we will define is the high load database access. In the window that appears locate the ‘database’ attribute and change the value to ‘Medium Load’ as pictured below.
Now click ‘OK’.
Rename the application Database, ‘Medium Load’ in the attributes table.
Now change the other fields to enter low load e-mail and web browsing. Note that web browsing comes under ‘http’ when selecting the application.
The finished application table should look like this, remember to name the applications.
Now click ‘Ok’.
You now need to enter the profile definition to generate application layer traffic. Right-click over the profile configuration and choose to ‘Edit Attributes’ from the menu that appears.
Click the mouse over the ‘value’ field for the ‘Profile Configuration’ attribute. A window will appear similar to that of the application definition table. This is the profile configuration table.
Change the number of rows to 3.
Change the profile names to ‘database, medium’, ‘web, light’ and ‘e-mail, light’.
Then edit the applications value and select the appropriate value from the applications we have defined. The finished applications table will look like this:
Click ‘Ok’ and exit to the network screen.
Creating Servers for the Network
Workgroup servers will be the source for all the traffic. There will be workgroup 4 servers, one in each of the subnets connected to the hubs using a 10BaseT link.
Each of the workgroup servers will need to be configured to tell Opnet which applications they will run. To reducer the amount of repetitive data entering we will set-up one server then copy and paste it into each location. This is possible because they are all going to serve the same applications.
The workgroup servers will provide e-mail and intranet access.
In subnet A, enter the hub subnet. In the object palate find the intermediate Ethernet server.
Now place one in the workspace and connect it to the hub using a 10BaseT link. Name the server Subnet_A_Server,
Right-click over the server and select the ‘Edit Attributes’ option.
In the attributes window click the mouse over the value field for the ‘Application: Supported Services’ attribute and select ‘Edit’ from the drop down menu.
You will now be presented with the application: supported services window. Change the number of rows to 2 then click over the name field and change the values to the applications for e-mail and web browsing that defined earlier. The window should now look like this:
Click ‘Ok’ and return to the subnet.
Now select the server node and from the ‘Edit’ menu select ‘copy’. Use the ‘Paste’ function to place a server in each subnet then connect them to the hubs using 10BaseT links.
Now place another server in the Switch subnet located in subnet A. use a 10BaseT link to connect it to the switch.
Now use the knowledge you have gained in this lab to configure the server to serve medium database access.
Finally before we can run our simulation we need to change the profiles for each of the Sm_Int_Wkstn’s to use the traffic we defined. To do this, enter one of the subnets and select all the Sm_Int_Wkstn nodes.
Now edit the attributes and check the box in the bottom left of the window to ‘Apply Changes to Selected Objects’. This will apply our changes to all the selected nodes.
Edit the ‘Application: Supported Services’ attribute and add 3 rows to the table to include all our traffic. It should look like this:
You will now have to repeat this for each of the subnets.
Running the Simulation
Right click on each server in turn and select to gather results for the server load (bits/sec) for each one.
Now select each of the point-to-point links between the routers and choose to collect results for the point to point utilisation in both directions.
Now run the simulation for 15 minutes.
Notice how long the simulation takes to run, this is because we are simulating a far heavier load of traffic than in lab 1 so Opnet takes a lot longer to calculate results.
How do you think the results for the server load an point to point utilisation will differ for each node and link? Why do you think this is?
The results for server load should resemble these.
As you can see from the results the load on the workgroup servers is far lower than that of the enterprise server. This is because they have to serve less data to fewer machines.
Now look at the results for point-to-point utilisation between subnets A and B, and subnets C and DE.
They should resemble this:
As you can see the utilization between subnets A and B is substantially higher than that between subnets C and DE. This is because all traffic for the enterprise server that is not going to subnet A crosses this link to supply subnets B, C and DE where only traffic to and from subnet DE crosses the link between subnets C and DE. Where the point-to-point utilisation reaches 100% the link is fully burdened with traffic. At these times traffic will take a long time to traverse the links.
Extension Work
Clear the traffic profiles you have created and set-up the network to use different traffic types. Investigate the demands of the varying traffic types place on the network.